Cybersecurity & Ethical Hacking
Master The
Art of Hacking
Ethically.
In-depth tutorials, free security tools, and expert resources for cybersecurity professionals and beginners alike.
100%
Free
Weekly
New Content
Expert
Authors
$nmap -sV -sC target.com
Starting Nmap 7.94 scan...
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9
80/tcp open http nginx 1.24
443/tcp open https nginx 1.24
$gobuster dir -u https://target.com -w wordlist.txt
✓ /admin (Status: 302)
✓ /api/v1 (Status: 200)
⚠ /backup (Status: 200) ← Investigate
$learn more at guardyk.com
// resources
Check Out Our Products
// services
Professional Penetration Testing Services
Protect your infrastructure with expert security assessments. We identify vulnerabilities before attackers do.
View All ServicesWhy Choose Guardyk?
Proactive Security
Find vulnerabilities before attackers exploit them
Certified Experts
Industry-recognized offensive security credentials
Detailed Reporting
Actionable insights with clear remediation steps
Compliance Ready
PCI DSS, HIPAA, GDPR & more
Average cost of a data breach in 2025
$4.44 Million
// knowledge base
All Tutorials
Latest Tutorials

Ethical Hacking
210
Target Fingerprinting for Client-Side Attacks
Before you launch a client-side attack, you need to know your target. This tutorial shows you how to fingerprint them using Canary Tokens and tracking images to capture their location, browser, OS, and more before you make a move.

Ethical Hacking
253
Finding and Using Public Exploits: A Practical Guide
From recon to root shell, learn how to locate, evaluate, and execute public exploits against vulnerable services. A practical reference for security enthusiasts.

Ethical Hacking
504
How to Install Kali Linux on VirtualBox
Learn how to install Kali Linux on VirtualBox step by step, even if it's your first time setting up a virtual machine. This guide covers both installing Kali using the ISO file and using the pre-built VM, so you can quickly create a safe environment for practicing cybersecurity and penetration testing.

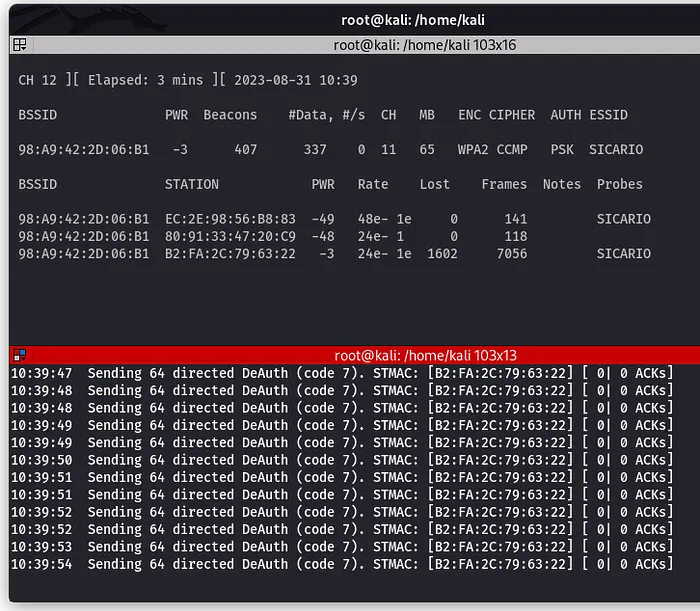
Network Hacking & Security
375
What Are Hosts in Cybersecurity?
This tutorial explains what hosts are in cybersecurity, why every network-connected device is a potential attack surface, and how attackers target them. It also covers defensive strategies like host hardening, EDR, patch management, and asset discovery to protect organizational networks.

Open Source Intelligence (OSINT)
534
The Dark Web: A Beginner's Guide to Accessing & Navigating It
The dark web sounds scarier than it is. In this guide, I show you how to access it using Tor, and take you on a tour of some of the wildest sites hiding beneath the surface of the internet.
Open Source Intelligence (OSINT)
730
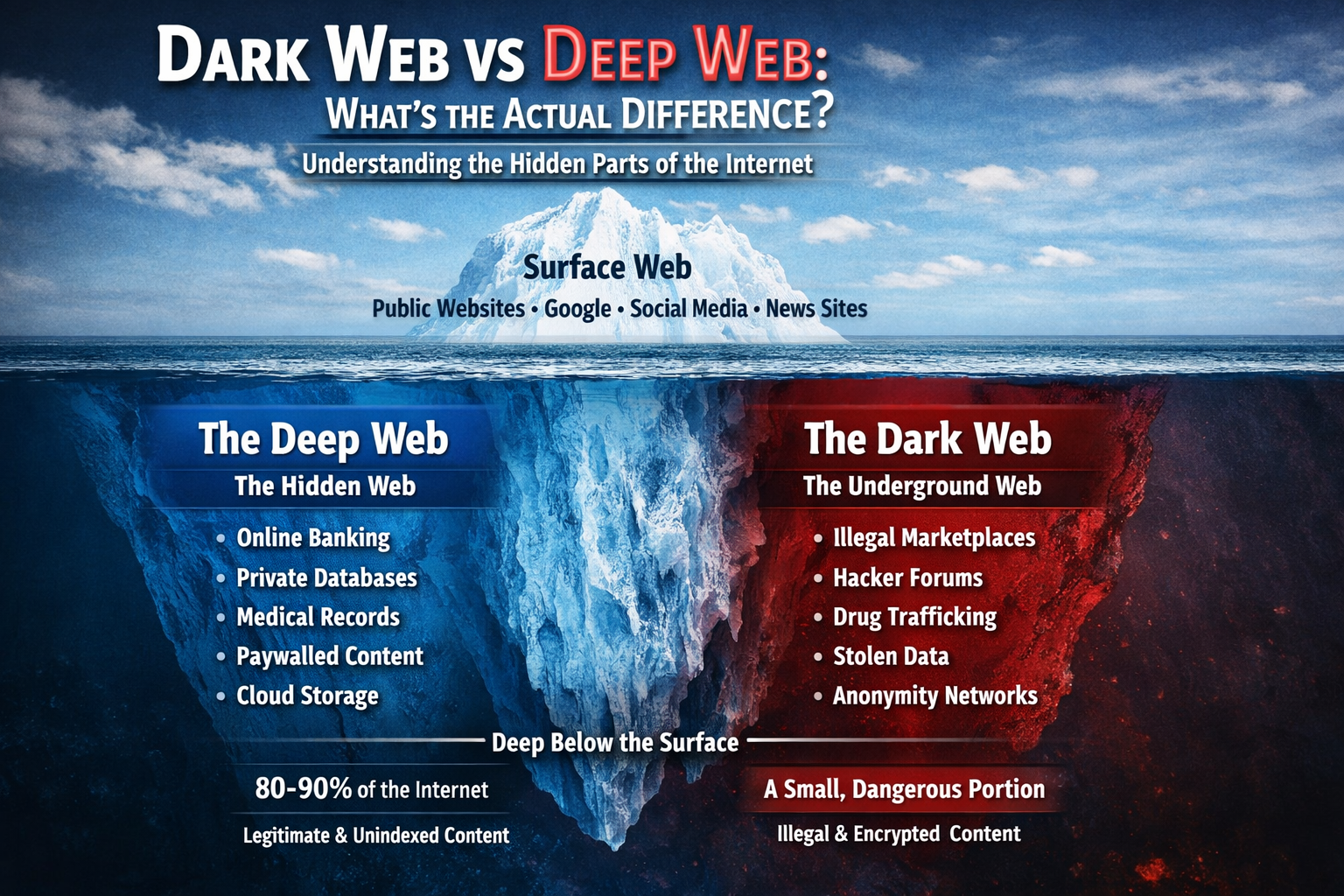
Dark Web vs Deep Web: What's the Actual Difference?
Confused about the dark web and deep web? You're not alone. Most people use these terms interchangeably, but they're completely different things. This guide breaks down the actual differences, size comparisons, and what you'll really find in each part of the hidden internet.

Open Source Intelligence (OSINT)
443
Searching for a Trafficked Person Using Open Source Intelligence (OSINT)
Learn how Open Source Intelligence (OSINT) can be used to locate missing or trafficked persons by analyzing publicly available data such as phone numbers, online ads, images, and social media traces. It explains real-world techniques, tools, and investigation strategies that turn scattered digital footprints into actionable leads.

Ethical Hacking
1.0k
How to Create and Use Wordlists for Password Testing
Learn to create and use wordlists for authorized password testing. This guide covers built-in wordlists like rockyou.txt, generating custom wordlists with Crunch, and understanding why password predictability matters for security.

Ethical Hacking
1.0k
Preparing for Your Next Web Pentest
A practical guide to pre-attack reconnaissance: setting engagement rules, Google dorking, discovering subdomains and endpoints, identifying tech stacks and WAFs, and mining JS files for secrets using tools like Subfinder, Wayback Machine, and Wappalyzer.
// utilities
All Tools
Free Security Tools
Password Breach Checker
Check if your password has been exposed in data breaches using secure K-anonymity technology.
Check Password
Password Strength & Generator
Analyze password strength and generate cryptographically secure passwords with customizable options.
Check Password
Encryption / Decryption Tool
Securely encrypt and decrypt text using industry-standard algorithms including AES-256 and RSA.
Encrypt / Decrypt

 Digital Forensics
Digital Forensics
 Ethical Hacking
Ethical Hacking
 Network Hacking & Security
Network Hacking & Security
 Open Source Intelligence (OSINT)
Open Source Intelligence (OSINT)