Muhammad Abdullahi
About
Muhammad Abdullahi, OSCP+, is an ethical hacker and security engineer. He enjoys breaking into systems (legally) and teaching others to do the same. For any inquiries, feel free to reach out.
8
Tutorials3496
Total ViewsPublished Tutorials

What Are Hosts in Cybersecurity?
This tutorial explains what hosts are in cybersecurity, why every network-connected device is a potential attack surface, and how attackers …

The Dark Web: A Beginner's Guide to Accessing & Navigating It
The dark web sounds scarier than it is. In this guide, I show you how to access it using Tor, …
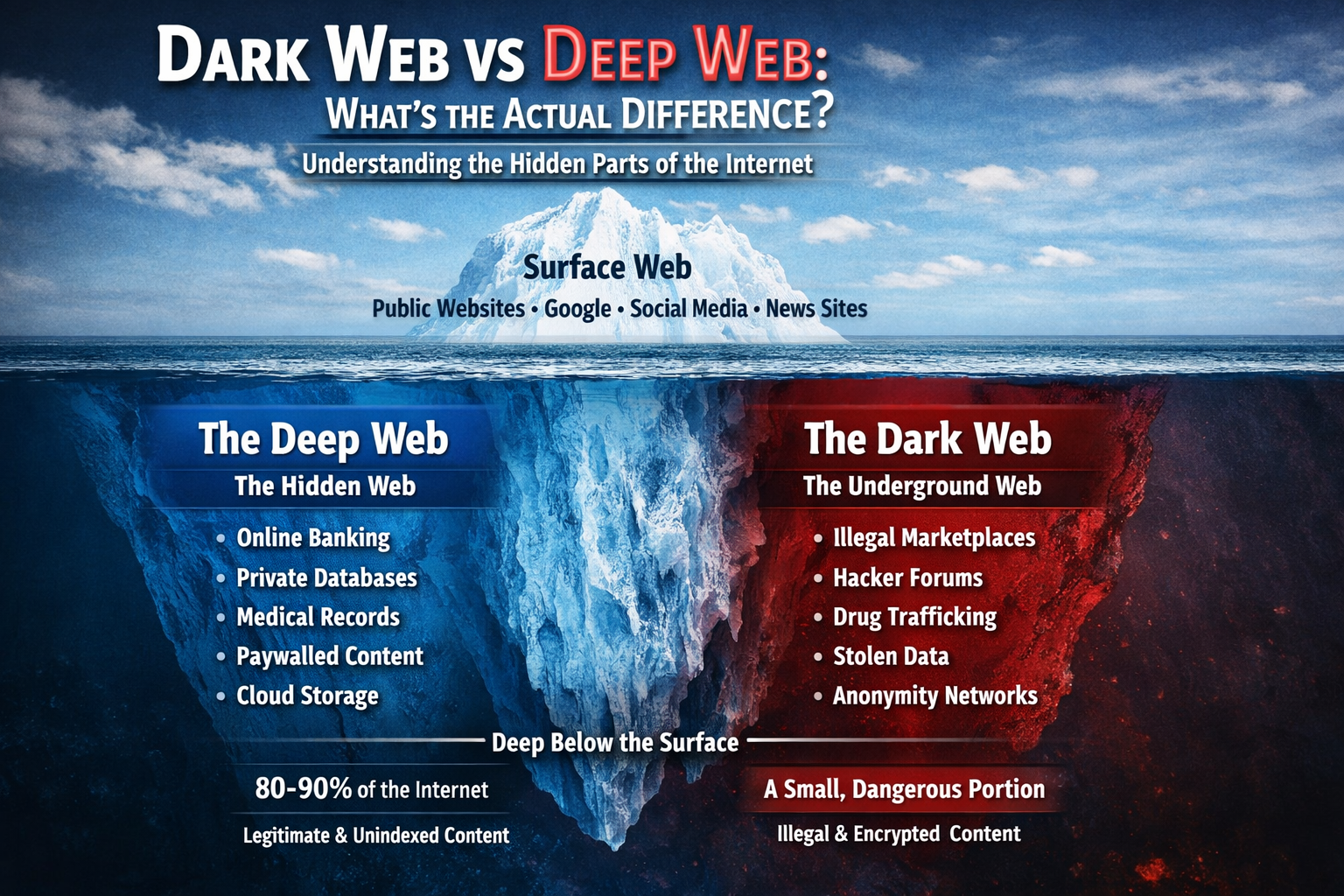
Dark Web vs Deep Web: What's the Actual Difference?
Confused about the dark web and deep web? You're not alone. Most people use these terms interchangeably, but they're completely …

Searching for a Trafficked Person Using Open Source Intelligence (OSINT)
Learn how Open Source Intelligence (OSINT) can be used to locate missing or trafficked persons by analyzing publicly available data …

How to Crack Locked PDFs
Learn how to crack password‑protected PDFs using pdfcrack. This concise guide covers PDF encryption basics, how pdfcrack approaches password cracking …
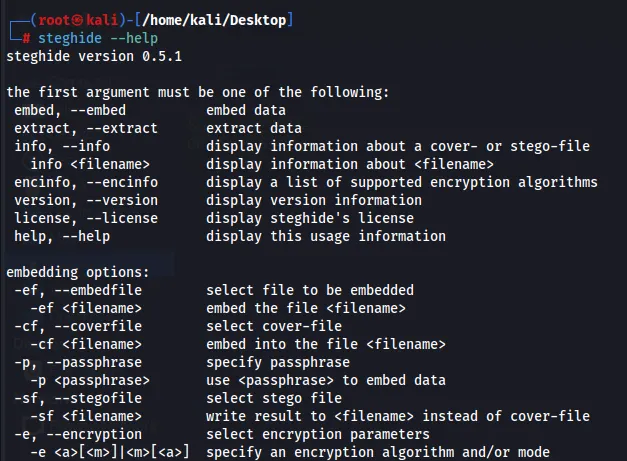
How to Hide Data in Plain Sight: Steganography Using Steghide
Learn to hide and retrieve data inside images and other files using steghide. This concise guide covers embedding/extraction, passphrase use, …
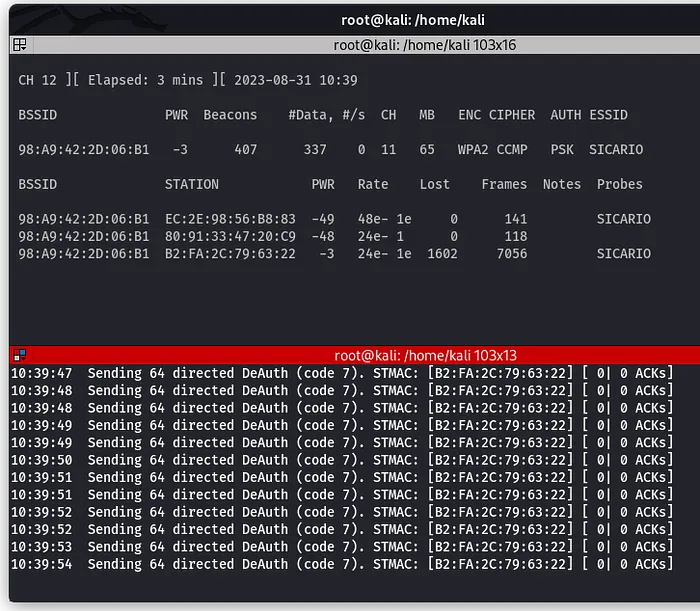
How to Perform a Wi-Fi Deauthentication Attack
Learn how Wi-Fi deauthentication attacks work and how targets can be forcibly disconnected from a network. This tutorial explains the …
How to Recover Deleted Files Using Foremost
Learn how to recover deleted files using Foremost, a powerful forensic tool for file carving. This guide walks you through …