// knowledge base
All Tutorials
Cybersecurity, ethical hacking & AI — all free, always.
Search & Filter
Ethical Hacking
1.9k
Step-by-Step Metasploitable2 Exploitation Guide for Penetration Testing and Vulnerability Assessment
A complete, beginner-friendly penetration testing tutorial for cybersecurity students, SOC analysts, and aspiring penetration testers.

Ethical Hacking
858
How to Crack Locked PDFs
Learn how to crack password‑protected PDFs using pdfcrack. This concise guide covers PDF encryption basics, how pdfcrack approaches password cracking and choosing wordlists.
Digital Forensics
1.3k
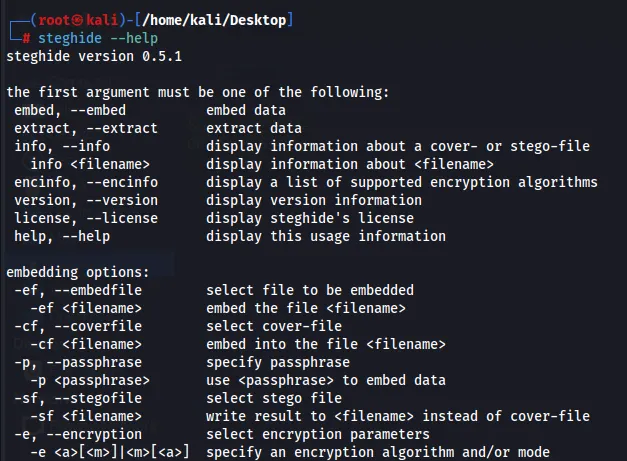
How to Hide Data in Plain Sight: Steganography Using Steghide
Learn to hide and retrieve data inside images and other files using steghide. This concise guide covers embedding/extraction, passphrase use, and safe, legal applications.
Ethical Hacking
Network Hacking & Security
724
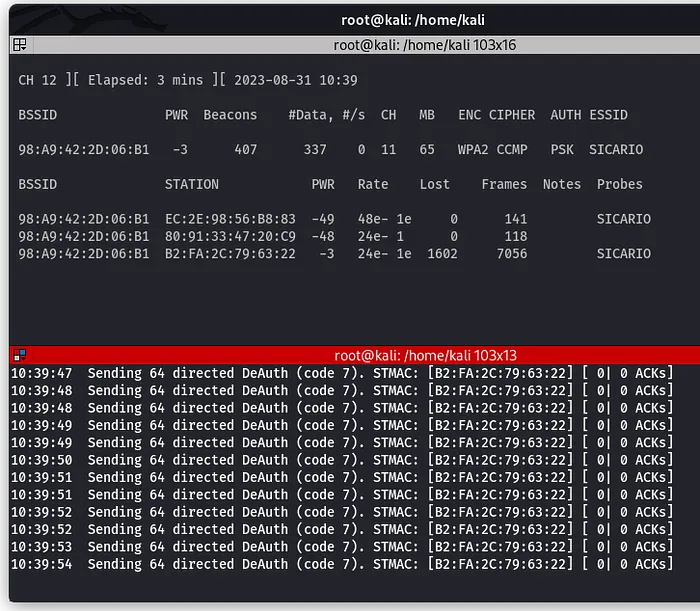
How to Perform a Wi-Fi Deauthentication Attack
Learn how Wi-Fi deauthentication attacks work and how targets can be forcibly disconnected from a network. This tutorial explains the concept and demonstrates the process in a controlled environment.
Digital Forensics
743
How to Recover Deleted Files Using Foremost
Learn how to recover deleted files using Foremost, a powerful forensic tool for file carving. This guide walks you through scanning storage devices for lost data and restoring deleted images, documents, and archives with ease.