Ethical Hacking
Learn to hack and secure systems the ethical way.
Ethical Hacking Collection
6 tutorials available in this category

How to Install Kali Linux on VirtualBox
Learn how to install Kali Linux on VirtualBox step by step, even if it's your first time setting up a virtual machine. This guide covers …

How to Create and Use Wordlists for Password Testing
Learn to create and use wordlists for authorized password testing. This guide covers built-in wordlists like rockyou.txt, generating custom wordlists with Crunch, and understanding why …

Preparing for Your Next Web Pentest
A practical guide to pre-attack reconnaissance: setting engagement rules, Google dorking, discovering subdomains and endpoints, identifying tech stacks and WAFs, and mining JS files for …
Step-by-Step Metasploitable2 Exploitation Guide for Penetration Testing and Vulnerability Assessment
A complete, beginner-friendly penetration testing tutorial for cybersecurity students, SOC analysts, and aspiring penetration testers.

How to Crack Locked PDFs
Learn how to crack password‑protected PDFs using pdfcrack. This concise guide covers PDF encryption basics, how pdfcrack approaches password cracking and choosing wordlists.
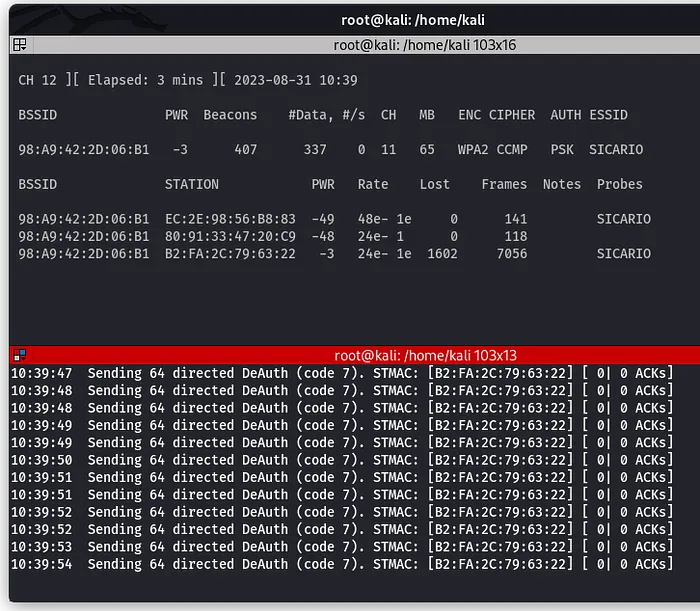
How to Perform a Wi-Fi Deauthentication Attack
Learn how Wi-Fi deauthentication attacks work and how targets can be forcibly disconnected from a network. This tutorial explains the concept and demonstrates the process …